5 minutes
MISP - High Availability with Amazon EKS
Summary
Ubisoft’s blue team introduces MISP K8S – an automated deployment of a high availability MISP instance using Kubernetes and AWS.
Introducing MISP-K8S
With special thanks to our talented security tool engineers Alexis Vuillaume and Jérémie Ben Arros we’re proud to announce a new addition to the MISP ecosystem — MISP-K8S.
MISP-K8S provides automated deployment of a scalable, high availability MISP + MISP-Dashboard Kubernetes cluster in AWS.
Last week Alexis Tremblay and I spoke at the Entertainment Software Association to introduce MISP-K8S and the role that MISP plays within Ubisoft’s blue team. We proposed next steps for making MISP a permanent feature of our industry’s landscape and spoke to Ubisoft’s commitment to provide training and technical support to the gaming community.
MISP-K8S aims to facilitate wider adoption of MISP in the gaming community. The project will continue to evolve as Ubisoft works with trusted industry partners to further develop our active sharing community.
We hope you will find it useful and welcome your feedback!
Inspired by HAMISPA
Tiago Faria presented HAMISPA project at the MISP Threat Intelligence Summit 0x05 back in October 2019 where he described the architecture of a high availability environment in AWS. His talk at the MISP Summit inspired us to build similar capabilities which have become the MISP-K8S project.
His work is ongoing and for those of you without an appetite to use EKS and Terraform, his MISP-cloud AMI may be an attractive alternative.
MISP-K8S
Skip this section if you don’t care how MISP-K8S works under the hood.
The basic K8S cluster is illustrated below.
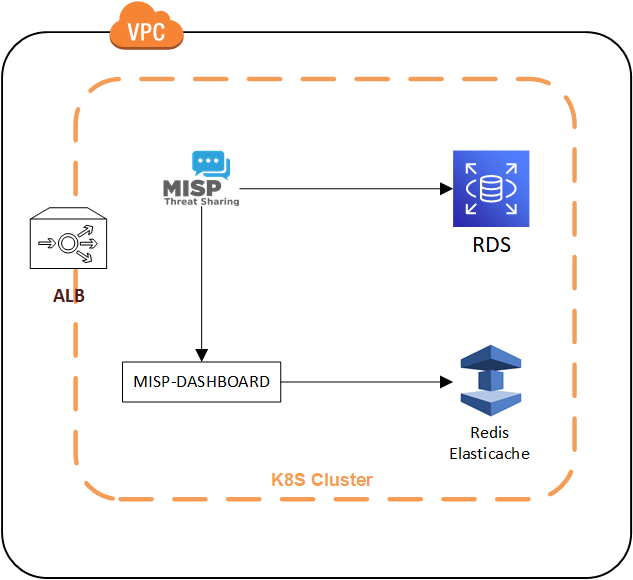
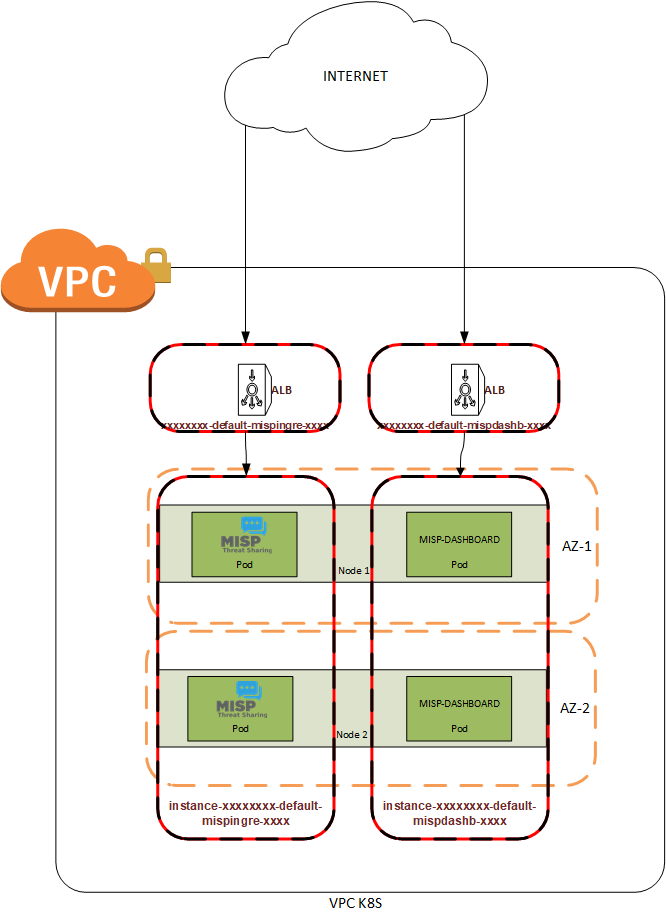
MISP-K8S uses Elastic Kubernetes Service (EKS) and each EKS cluster is load-balanced with ALB. Each cluster contains ephemeral MISP and a MISP Dashboard nodes. Each node’s security group allows HTTPS ingress and the certificate is managed by Route53 as is the corresponding node’s DNS entry.
MISP Dashboard is enabled by default with mandatory user authentication. Be sure to add the correct account permissions in order to use this feature.
For better assurance that threat data is neither lost nor unavailable we’ve swapped out the default MISP Maria db for AWS RDS which handles high-availability and backups for us.
Similarly, MISP Dashboard’s local Redis instance has been replaced with Elasticache. This provides better assurance against the loss of MISP Dashboard Internet points.
RDS + Elasticache give us some great benefits; they use multiple availability zones, the backups are managed by AWS, and everything scales very quickly. Everything important is stored in RDS and Elasticache or written at run time as a Docker/Terraform variable. This let’s us shut down, destroy or update our containers without having to worry as much about recovery.
Clusters are distributed across multiple availability zones as illustrated below.
Gamify All The Things!
Working for a game studio is pretty great. Lots of creative people. In a cafeteria or lounge I’ll overhear random heated exchanges professing our bondage within a simulation or that systemd is shit. It’s totally my jam.
Infosec at a game studio is especially interesting because the creative culture gives us license to experiment with new things. Magical things. Dangerous things. Cyber threat intelligence as a game things.
And who better than a game studio to experiment with gamification? With so much knowledge and talent at our fingertips it would be a waste not to get a little weird. So our team at Ubisoft is pressing forward with MISP Dashboard to see where it takes us, to find whatever untapped collaborative potential exists within the threat intelligence community of the gaming industry.
It may sound like it’s all fun and games but it’s also serious business; if done poorly we incentivize maladaptive behaviour. Like submitting trash intel to inflate reputation, or viewing Internet points as an end in themselves. We need to be mindful of what we’re awarding points for and what the target of our effort really is.
So how can an ISAO use gamification, and more generally the data that MISP Dashboard aggregates from industry partners?
Firstly, prioritize achievements (in MISP Dashboard, “badges”) over points, and award badges for acts that feed value back into the community such as deep-dive threat intel reports, assessments of high-priority industry threats, trainings and development/integration assistance.
Secondly, use industry trends to inform strategy. Create incentive to research new and poorly understood threat actors, their malware, and techniques.
An ISAO grants unique opportunity to understand how industry partners, and the industry as a whole, interact with a threat actor. Where some ISAO members may struggle to produce any actionable intel on a sophisticated actor or malware, others may be better equipped to keep pace. Identifying which organizations produce intel on high-priority actors, and the type of intel they produce, guides training and knowledge sharing opportunities.
Lastly, sharing is caring. Build a culture of sharing and don’t be afraid to get a little preachy about herd immunity; CTI data is lowest common denominator within an ISAO but the real goal is to make the entire industry less attractive to attackers by increasing attacker costs. Consider that rather than independently grinding out content, partners should consolidate their effort by sharing Atomic Threat Coverage playbooks, YARA rules, SIGMA rules, and any security content not at odds with the business model.
Award points and badges for sharing content and by improving the capabilities of industry partners everyone wins.
Next Steps
MISP-K8S is in active development. For now we’re using multiple availability zones within the same region; we’re exploring the idea of making MISP-K8s available across multiple regions, as well as using GCP and KVM as deployment options rather than being vendor locked in AWS.
If you wish to request a feature, or report a bug, please open an issue on Github.
Thanks to everyone on our team who participated in making this project a thing!